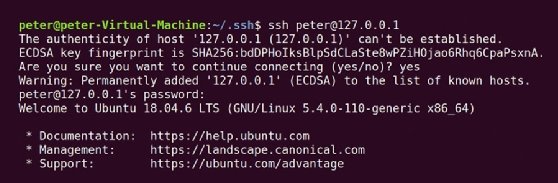
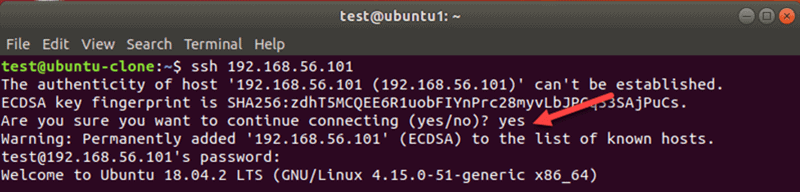
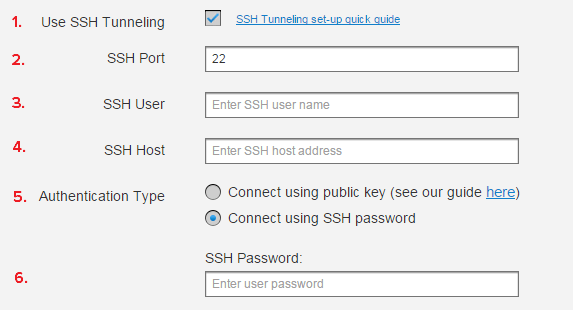
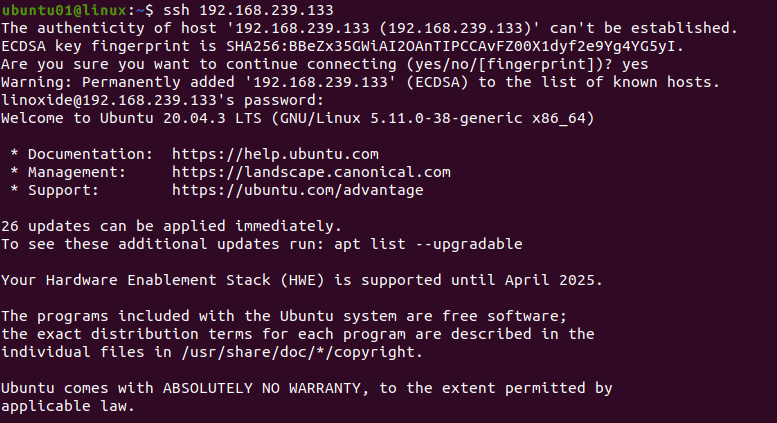
Linux/Unix: Force ssh client to use only password auth authentication when pubkey auth configured - nixCraft
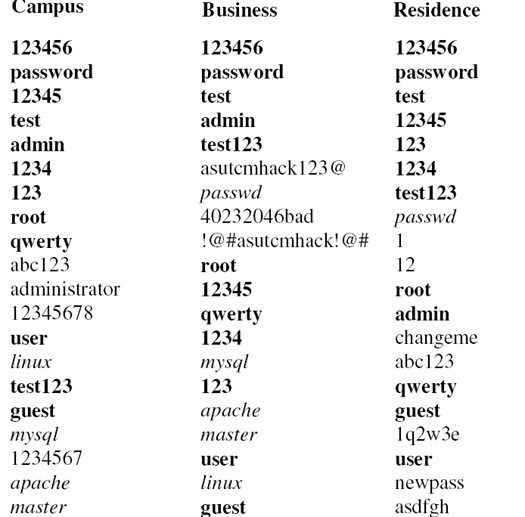
GitHub - jeanphorn/wordlist: Collection of some common wordlists such as RDP password, user name list, ssh password wordlist for brute force. IP Cameras Default Passwords.